Adapting to Quantum Computing: The Future of Secure Software in LA
Understanding the Threat of Quantum Computing to Software Security in Los Angeles
The emergence of quantum computing heralds a new era of computational power, one that holds the potential to break the very backbone of current cryptographic systems. As a premier software development agency in Los Angeles, Bee Techy is at the forefront of addressing these looming challenges. The National Security Agency emphasizes the importance of quantum-resistant cryptography over traditional quantum key distribution (QKD) or quantum cryptography (QC) methods, recognizing the need for a more robust defense against quantum attacks.
Quantum computing’s threat to software security is not a distant concern; it’s a present reality that demands immediate attention. The cryptographic algorithms that secure our data today rely on the difficulty of certain mathematical problems, which quantum computers can solve with alarming efficiency. This capability exposes vulnerabilities in systems across Los Angeles, from financial institutions to healthcare providers, making quantum-resistant encryption not just an option, but a necessity.
At Bee Techy, we understand that the city’s digital infrastructure is only as strong as its weakest link. The integration of quantum-resistant encryption is a critical step in safeguarding Los Angeles’s status as a hub of innovation and economic growth. The transition to these new cryptographic standards will ensure the longevity and security of software applications in the quantum age.

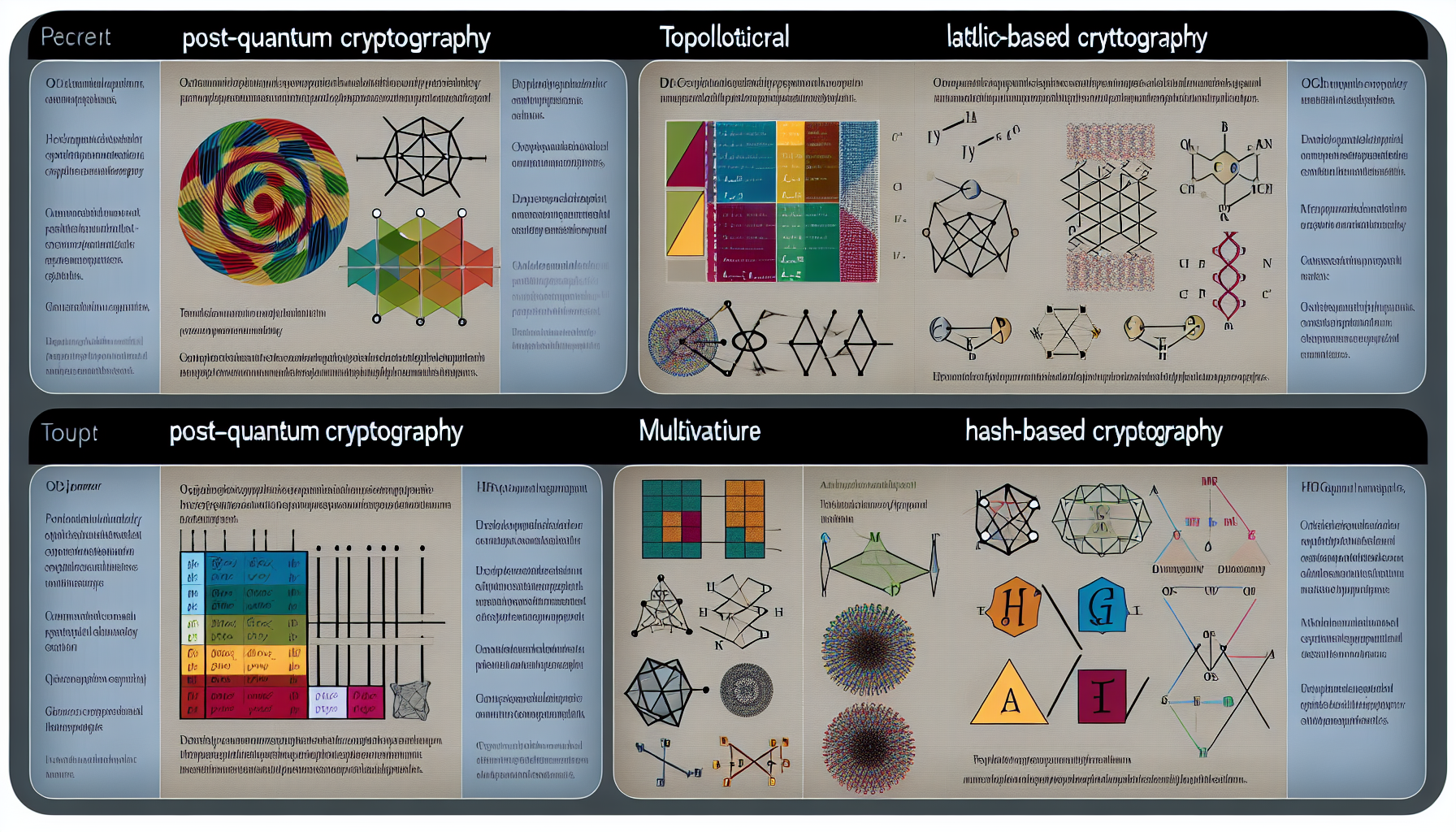
Selecting Post-Quantum Cryptography Algorithms for LA-Based Applications
The selection of post-quantum cryptography (PQC) algorithms is a task that requires deep technical expertise and foresight. The National Institute of Standards and Technology (NIST) recently announced the first four quantum-resistant cryptographic algorithms, marking a significant milestone in the evolution of digital security. These algorithms are designed to withstand the onslaught of quantum computational attacks, ensuring that applications remain secure in the post-quantum world.
The four pioneering algorithms include lattice-based, hash-based, multivariate quadratic equations, and code-based solutions. They are selected for their robustness against quantum computing’s advanced capabilities, providing a shield for the confidentiality, integrity, and authenticity of digital communications in Los Angeles. It’s not just about choosing an algorithm; it’s about selecting the right one for the specific needs of an application, be it for general encryption or digital signature generation.
At Bee Techy, our team of experts specializes in integrating these cutting-edge post-quantum cryptography algorithms into custom software applications. We ensure that our clients in LA are equipped with the most advanced and suitable cryptographic defenses, tailored to their unique operational requirements and business objectives.
Secure Software Development 2024: Best Practices for Quantum Computing Security
The landscape of secure software development is rapidly evolving, and as we move into 2024, the integration of best practices for quantum computing security becomes paramount. A recent publication by Security Intelligence Magazine, titled “The CISO’s Guide to Accelerating Quantum-Safe Readiness”, provides invaluable insights for Chief Information Security Officers striving to fortify their organizations against quantum threats.
One of the essential steps in this journey is the discovery and documentation of organizational cryptography. This process involves taking stock of all cryptographic assets and assessing their vulnerability to quantum attacks. Once identified, the path to migrating to safer alternatives becomes clearer, allowing for a structured and efficient transition to quantum-resistant cryptographic solutions.
The guide also underscores the importance of equipping security teams with the necessary tools and education to test new cryptographic protocols. At Bee Techy, we embrace this directive by providing comprehensive training and resources to our developers, ensuring that the software we create not only meets but exceeds the stringent security standards expected in the quantum era.
Protecting Against Quantum Attacks LA: Quantum-Resistant Encryption Implementation
As the reality of quantum attacks looms over Los Angeles, the implementation of quantum-resistant encryption becomes a critical defense strategy. CyberDefenseMagazine.com’s article, “Steps for Preparing for a Quantum-Resistant Cryptographic Future”, highlights the necessity of adopting these advanced cryptographic measures.
The four quantum-resistant algorithms endorsed by NIST are based on mathematical problems that pose a significant challenge to both classical and quantum computers. This dual resistance is crucial for ensuring that software applications remain secure against both current and future threats. The implementation of these algorithms is not a mere upgrade; it’s a fundamental shift in how we protect digital assets.
At Bee Techy, we don’t just follow trends; we set them. Our proactive approach to implementing quantum-resistant encryption ensures that our clients’ applications are not only prepared for quantum attacks but are also built on a foundation of forward-thinking security practices.
Performance Optimization for Quantum-Resistant Applications in Los Angeles
The transition to quantum-resistant applications is not without its challenges. One of the primary concerns is the potential impact on performance. However, at Bee Techy, we understand that security should not come at the expense of efficiency. We specialize in optimizing the performance of quantum-resistant applications to ensure they operate seamlessly within the fast-paced environment of Los Angeles.
Our optimization process begins with a thorough analysis of the application’s architecture, identifying areas where quantum-resistant algorithms can be integrated without compromising speed or user experience. We then implement strategic enhancements to maintain, and in many cases improve, the performance of the application post-integration.
Our commitment to excellence in both security and performance is what sets Bee Techy apart as a leader in software development. We ensure that our clients receive a product that not only stands up to the quantum threat but also excels in its operational capabilities.
Are you ready to future-proof your software against the quantum threat? Visit https://beetechy.com/get-quote to contact us for a quote and take the first step towards secure, quantum-resistant software development in Los Angeles.